Processadores possuem instruções não especificadas
Breaking the x86 instruction set, Christopher Domas, Blackhat 2017
A processor is not a trusted black box for running code; on the contrary, modern x86 chips are packed full of secret instructions and hardware bugs. In this talk, we'll demonstrate how page fault analysis and some creative processor fuzzing can be used to exhaustively search the x86 instruction set and uncover the secrets buried in your chipset. We'll disclose new x86 hardware glitches, previously unknown machine instructions, ubiquitous software bugs, and flaws in enterprise hypervisors. Best of all, we'll release our sandsifter toolset, so that you can audit - and break - your own processor.
Como testar uma implementação x86?
- Existem inúmeros decodificadores de instruções x86 em software
- Eles não concordam em todas as instruções!
- Para instruções documentadas, executar a instrução em um simulador (QEmu) e comparar os resultados
- Para instruções não documentadas, anotar o resultado antes e após a instrução (registradores e status)
Como descobrir instruções não documentadas?
- Primeiramente tentar descobrir o tamanho delas
- Comece pelas menores (1 byte) e vá explorando os tamanhos
- Não é necessário explorar os múltiplos registradores
- Instruções não especificadas não geram unknown instruction trap
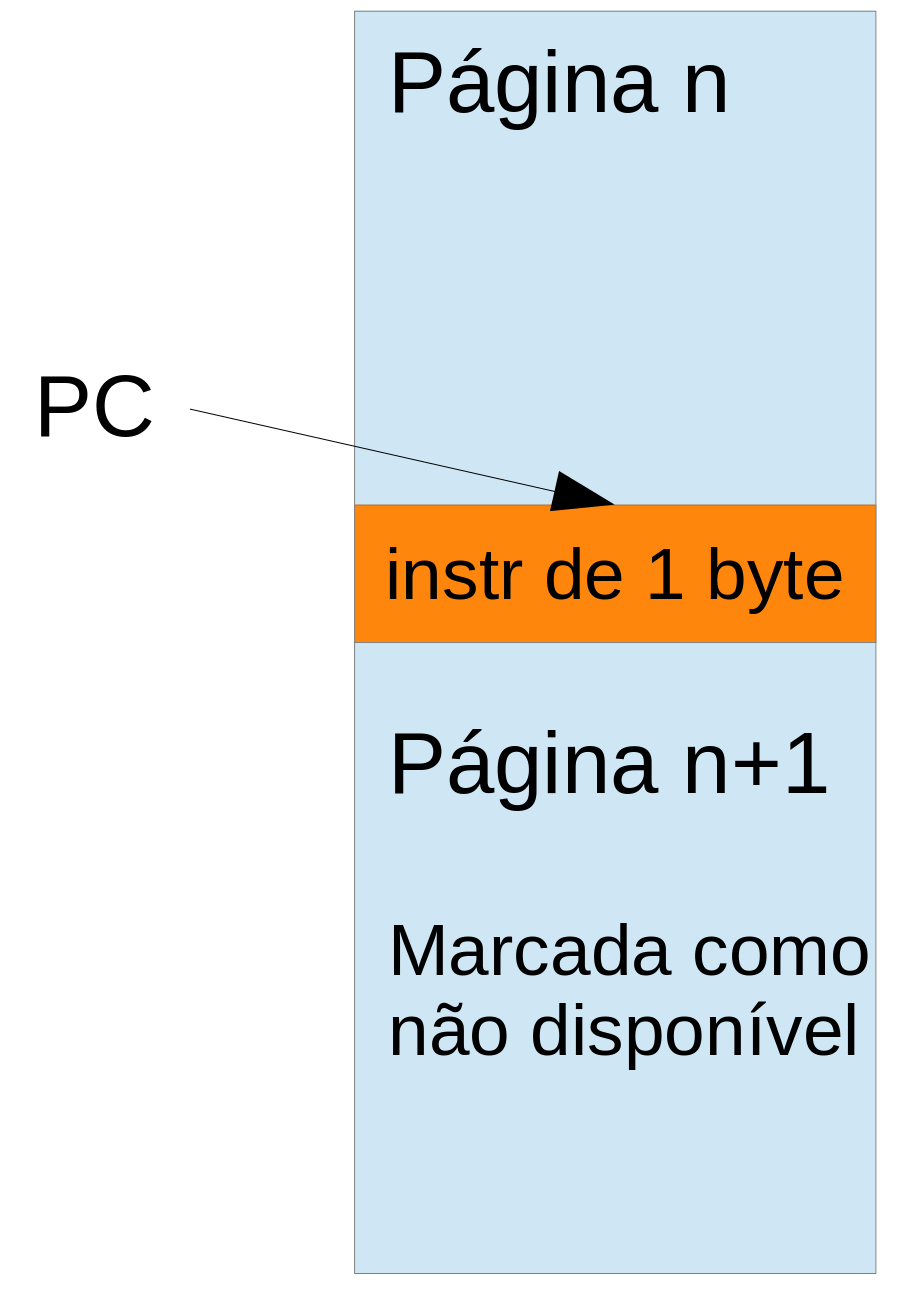
- Coloque uma instrução no final de uma página e configure a próxima página como não disponível
- Utilize page faults para detectar o tamanho das instruções
Exemplo
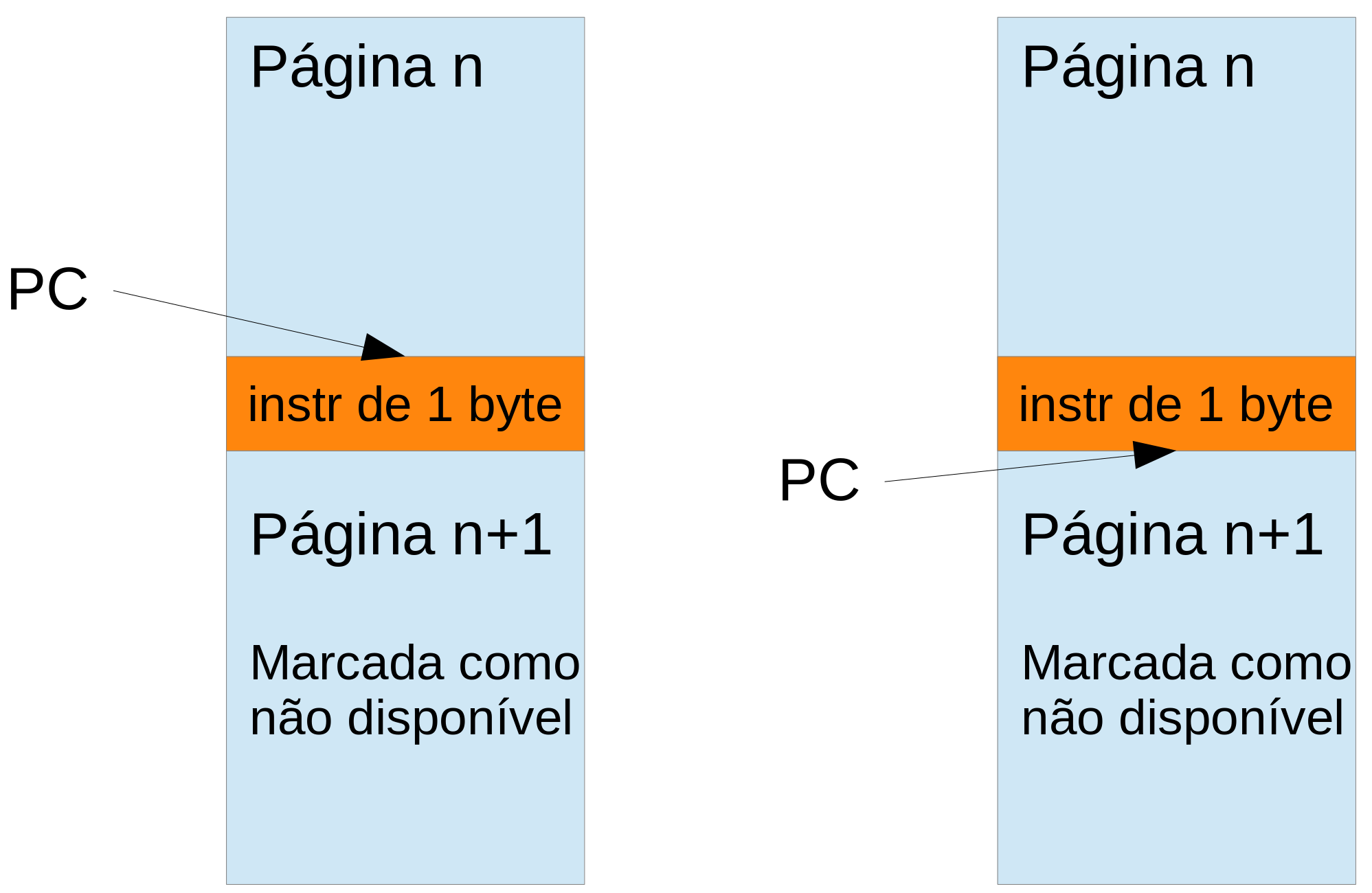
Qual trap vai acontecer? Instrução inválida ou page fault?
Exemplo
Exemplo para 2 bytes
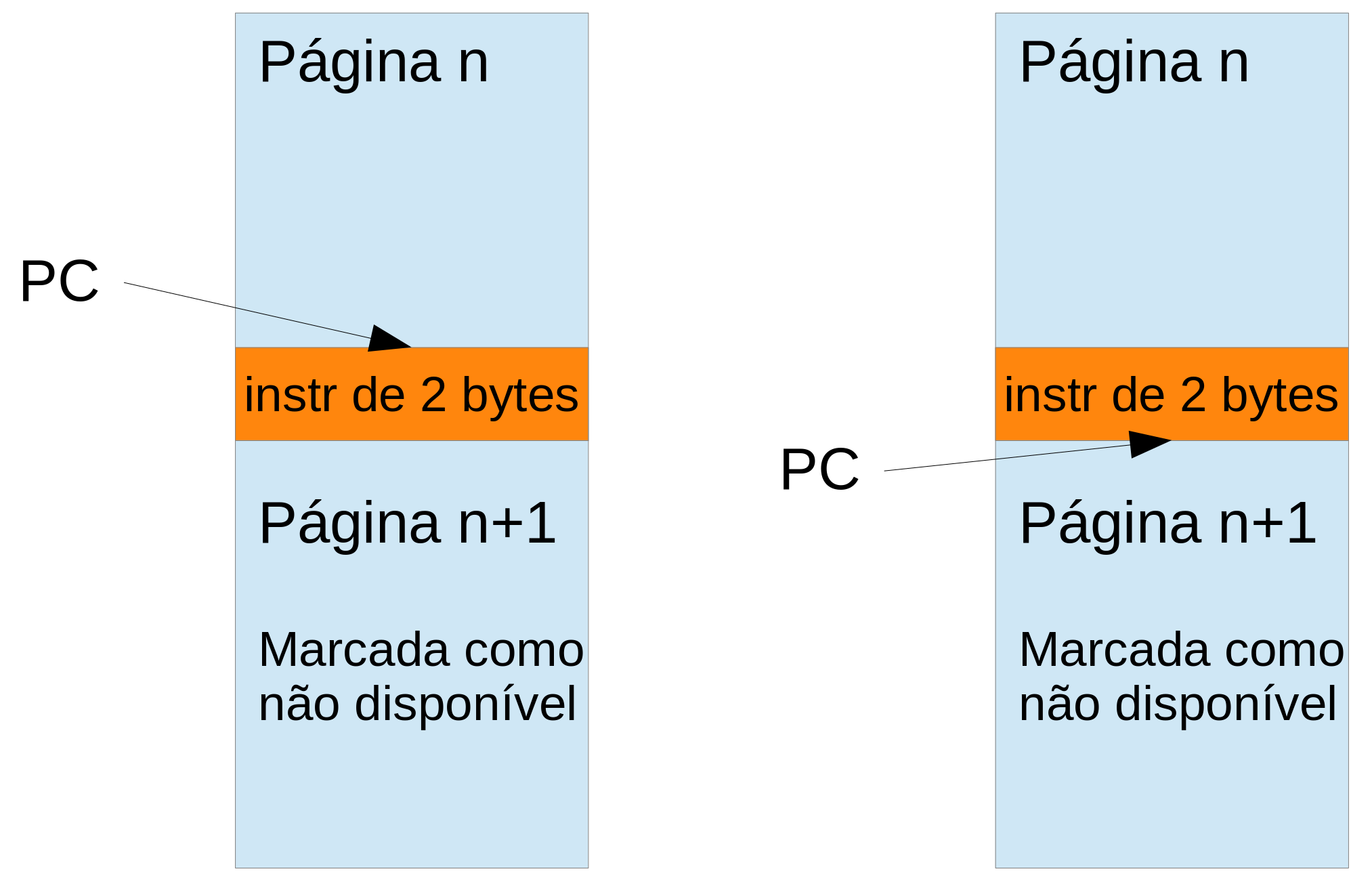
Aumente o tamanho em bytes enquanto for indicado que aconteceu page fault
Como verificar o comportamento?
- Dado o código
main() {
int i, v[10];
for (i = 0; i < 10; i++)
v[i] = i;
}
- Não importa em qual processador está executando, o programa:
- executa 10 vezes o laço
- escreve 10 vezes na memória
- escreve os números de 0 até 9 na memória
HybridVerifier. Embedded Systems Letters, 2017
Conjuntos de instruções envelhecem
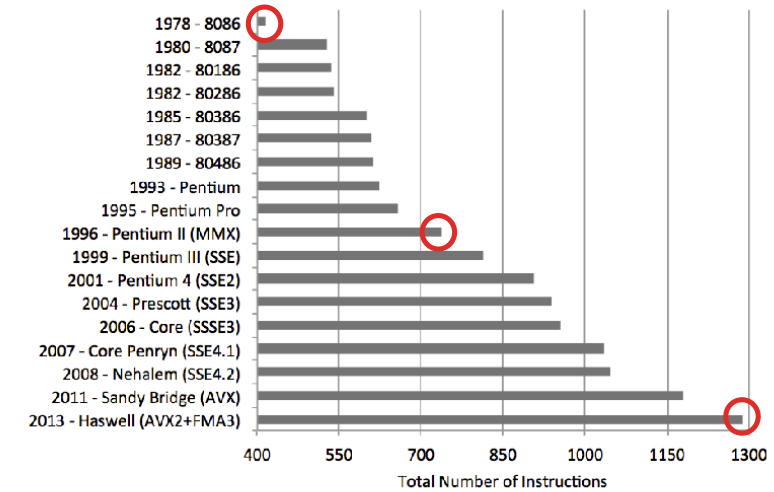
SHRINK: Reducing the ISA complexity via instruction recycling. ISCA 2015
Ter muitas instruções aumentam o tamanho do código
- Os mesmos programas (SPEC 2006) foram compilados para múltiplas arquiteturas
- Note que o menor código não é uma arquitetura CISC!
Ecco, SBAC-PAD 2009